On February 7, the government cybersecurity and intelligence agencies of the United States, United Kingdom, Australia, Canada and New Zealand said the Chinese government has for years been carrying out cyber operations, with state hackers “seeking to pre-position themselves on IT networks for disruptive or destructive cyberattacks” against their nations’ critical infrastructure.
On February 5, the Philippine government said it had warded off cyberattacks from China targeting the websites and email systems of President Ferdinand Marcos Jr. and various government agencies.
A government spokesperson told local media that they are not attributing hacking activities to any specific state but have traced the attack to an undisclosed location in China.
On February 6, Dutch intelligence agencies disclosed that Chinese state-backed cyber spies gained access to a Dutch military network in 2023. It is the first time the Netherlands has publicly attributed cyber espionage to China.
In response, the Chinese Embassy in the Philippines and the Chinese Embassy in the Netherlands dismissed the accusations in identically worded statements:
“The Chinese government … allows no country or individual to engage in cyber attacks and other illegal activities on Chinese soil or using Chinese infrastructure.”
That is false.
China has a documented history of malicious and espionage cyber attacks around the world, most of which are linked to Chinese government actors.
The most notorious Chinese state cyber actors include:
Volt Typhoon
(Aka: Vanguard Panda, BRONZE SILHOUETTE, Dev-0391, UNC3236, Voltzite, Insidious Taurus)
In May 2023, Microsoft detected and identified Volt Typhoon as a Chinese state-sponsored actor. Volt Typhoon has been active since mid-2021 targeting the United States’ critical infrastructure. “[T]he affected organizations span the communications, manufacturing, utility, transportation, construction, maritime, government, information technology and education sectors,” Microsoft said.
The cybersecurity company CrowdStrike traced Volt Typhoon’s activities in the U.S. back to “at least mid-2020” and said one of the group’s tradecraft tactics was masquerading as a “legitimate IT help desk software.” This allowed the Chinese hackers to conduct “advanced intrusions” and stay undetected.
Microsoft also reported that Volt Typhoon’s stealthy activities included the use of a sophisticated technique known as “living off the land,” by which the invaders leave no traces of their presence on the disks and are nearly invisible to antivirus systems.
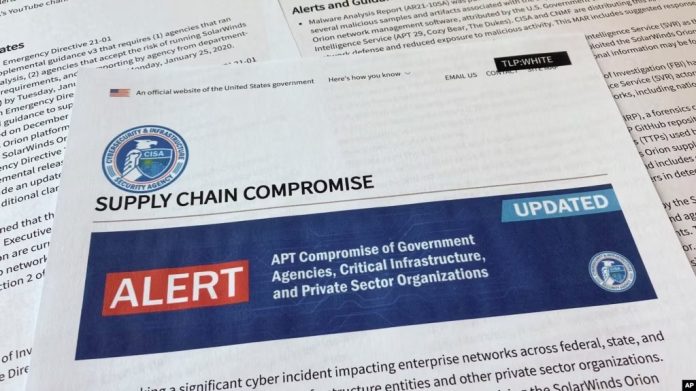
Volt Typhoon’s “choice of targets and pattern of behavior is not consistent with traditional cyber espionage or intelligence gathering operations,” the U.S. Cybersecurity and Infrastructure Security Agency, or CISA, said in a February 7 public cybersecurity advisory.
“The U.S. authoring agencies are concerned about the potential for these actors to use their network access for disruptive effects in the event of potential geopolitical tensions and/or military conflicts,” the CISA advisory said.
STORM-0558
Ahead of U.S. Secretary of State Antony Blinken’s trip to Beijing in June 2023, state-backed Chinese hackers dubbed Storm-0558 hacked the email accounts of U.S. government officials at multiple U.S. agencies that deal with China.
The hacked officials included Commerce Secretary Gina Raimondo, whose agency is in charge of imposing export controls on foreign markets. The United States currently maintains a sweeping set of export controls aimed at limiting the transfer of advanced computing and semiconductor manufacturing items to China.
Microsoft later admitted that the Chinese hackers used a “stolen Microsoft account consumer signing key to forge authentication tokens for Outlook Web Access and Outlook.com. The attackers also exploited a token validation issue to impersonate Azure Active Directory users and gain access to their email.”
Storm-0558 maintained access to email accounts of “about 25 organizations, including government agencies, since mid-May,” the report said.
APT 41
(Aka: Amoeba, BARIUM, BRONZE ATLAS, BRONZE EXPORT, Blackfly, Brass Typhoon, Earth Baku, G0044, G0096, Grayfly, HOODOO, LEAD, Red Kelpie, TA415, WICKED PANDA, WICKED SPIDER)
APT 41 is the most notorious hacker group identified as part of the Chinese Communist Party cyber espionage apparatus, whose members often pose as rogue actors. Cybersecurity watchdogs trace the groups’ activities back to at least 2012.
Its “favorite” tactics include spear phishing, water holes, supply chain attacks and backdoors, the U.S. Office of Information Security said in a September 2022 report detailing the group’s recent activities, which reach across at least 14 countries.
In 2019, the cybersecurity company FireEye Threat Intelligence assessed “with high confidence that APT41 is a Chinese state-sponsored espionage group that is also conducting financially motivated activity for personal gain.”
“The group has established and maintained strategic access to organizations in the health care, high-tech and telecommunications sectors,” the report said.
In 2020, the U.S. Justice Department brought charges against five Chinese nationals and two Malaysians with connections to APT 41, for hacking into more than 100 companies across the world to steal proprietary source code, customer data and other valuable business information.
According to the FBI arrest warrant for five members of APT 41, the group had conducted illegal cyber activities in “Australia, Brazil, Germany, India, Japan and Sweden, the United States, Australia, China (Tibet), Chile, India, Indonesia, Malaysia, Pakistan, Singapore, South Korea, Taiwan and Thailand.”